Start Left™'s Security Monitoring Capability:
The patented Behavioral Analytics Engine that centralizes, analyzes & correlates data insights.
Tap into the potential of your data and witness automated discovery of crucial insights that speed up security measures, eliminating the need for lengthy manual analysis. Our cutting-edge AI-driven security monitoring keeps an eye on human activities and behaviors to detect toxic combinations, risk scenarios, risk combinations, and threat predictions without the need for extra resources.
Without a centralized view, monitoring, investigations, and response capabilities are limited.
Start Left™'s platform tackles the challenge of limited centralized visibility, empowering your team's security actions with modern security analytics. Our patented Behavioral Analytics Engine and automated risk modeling integrated into your products, leverages real-time machine learning (ML) to easily connect the dots, identify threats, and prioritize them across your CI/CD and cloud data.
By fostering collaboration among your security, development, operations, and GRC teams through extensive data correlation, our platform provides valuable insights. With Start Left™'s security monitoring, you can make informed decisions and proactively address security challenges, all within a centralized hub for monitoring, investigations, and response capabilities.
Challenges Solved
Real-time visibility and anomaly detection
Go beyond code vulnerability scanning and uncover unknown risks and threats. Leave your worries behind with automatic risk detection to save time and boost productivity.
Detect risks and threats that matter
Say goodbye to information overload and alert fatigue. Streamline your workflows by eliminating false positives and focusing on what truly matters.
Priortize alerts
Empower your security and DevOps teams for rapid issue resolution. Access comprehensive incident context in a single unified platform.
Get a demo!
Learn how Start Left™ reduces blind spots and helps you gain control of cloud product security in under half an hour.
Tell us a little about your organization and we'll connect you with an expert who can share Start Left™'s behavior analytics and answer any questions you have.
Contact Us
Your unified security operations platform with pre-built detections.
You can only get so far with point solutions and security scans. Our Behavior Analytics Engine frees your most expensive resources from having to manually investigate with pre-built detections across tools and time. Let us handle putting your data to work for you so your people can focus on security outcomes.
Toxic Combinations
From the perspective of cloud product security, data analytics illuminates toxic combinations, for example: an app is publicly accessible, it handles sensitive data subject to PCI DSS regulations, it has a large user base, the Product Team has low visibility into their process risks, there are a large number of vulnerabilities present......
High Impact Opportunities
For vulnerability management, our security analytics automatically prioritizes high-impact opportunities, for example, where a Common Vulnerabilities and Exposures (CVE) is a level 7 and is highly exploited, affects 100 products across the entire product portfolio is considered more crucial to fix than a CVE that is a level 10 and only affects 1 product.
Most Improved Product / Team
Our analytics constantly track a variety of indicators on to highlight product teams that have successfully improved their risk management and where they still need to focus their efforts. They pertain to reducing risks over time through monitoring integrations, risk remediation performance, security hygiene, and team performance on each product team.
Risk Scenarios
Security monitoring automatically detects risk scenarios in cloud product security that include the accidental exposure of critical information, IP, or resources, as well as the illegal access of malicious actors, examples include: inadequate access control, segmentation, and cloud security, as well as a code repository that has been accidentally made public.
Risk Combinations
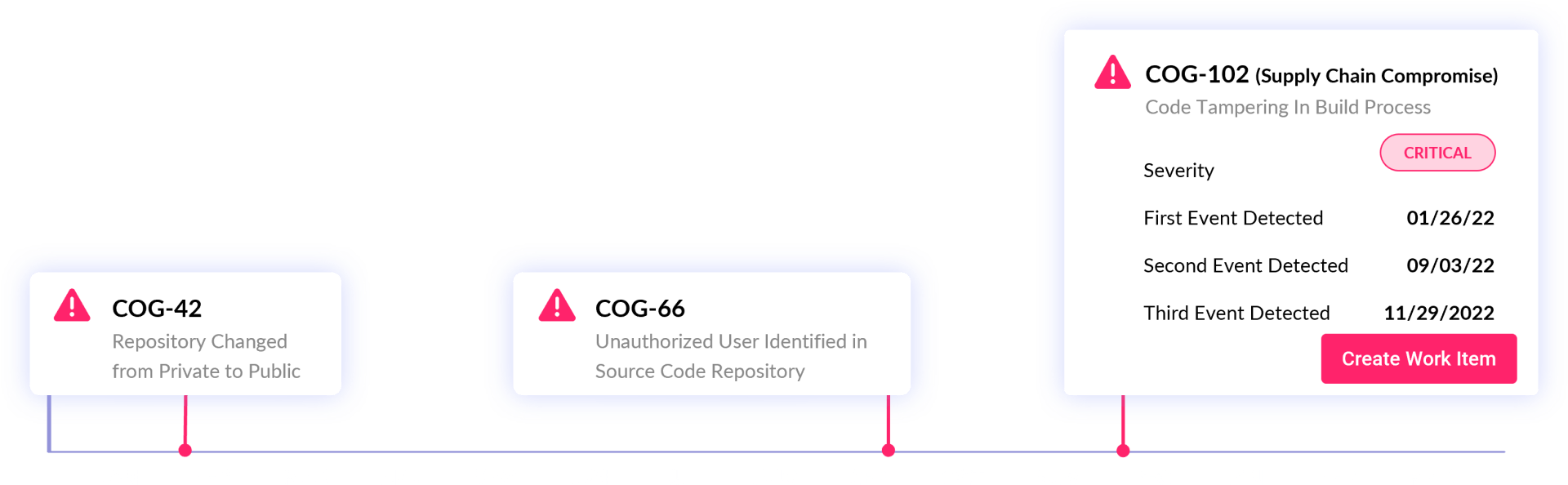
When numerous risk scenarios are present in tandem or correlated over time, it poses a risk combination. For example, supply chain compromise: in September 2022, detection of a team's code private repository changes to public, and in January 2023, detection of build process tampering, both events correlated by Start Left™ and raised as alert.
Threat Predictions
Comprehensive protection is completed with full lifecycle security monitoring and analytics to enhance actions by correlating patterns across all risk data in real time. This technique highlights which high-risk assets are likely to be compromised and direct attention there, especially with an active attacker present and can easily switch targets.
End-to-End Visibility & Threat Detection Benefits
Improved Security Posture
By automating cognitive security analytics through Start Left™'s technology, reduce the time and effort required to investigate and effectively respond to risks and active threats.
Eliminate inefficiencies
Our experts' knowledge is out-of-the-box, and our Cognition database is growing. No coding is required for detection, prioritization, actionable insight & learning content.
Discover the unknowns
Start Left™'s risk model correlates threat signals and behaviors. Connect real-time and historical data to package contextual signals for teams to take action.
Connect and start reaping the benefits in no time.
Our no-code API makes it a breeze.
Get a demo
Our no-code API makes it a breeze.






